Rethinking the nature of risk associated with disclosure of personal information

• We are all subject to risks when we disclose information about ourselves on social media and other online services
• These risks are balanced against the benefits of signing up to social media
• The decisions that individuals make when they sign up to social media can be described by a ‘privacy calculus’ model
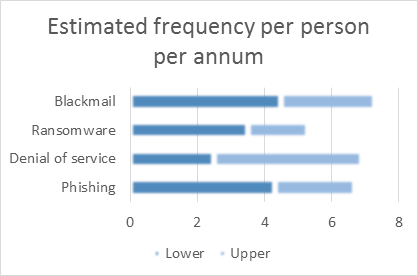
• Many attempts have been made to identify the risks and benefits of online services and to categorise them
• The objective of this research is to gather empirical data to support/challenge established risk models and to produce a more robust model for estimating risk levels
This study uses several methods to look at individual online behaviour in order to identify what personal data is disclosed during online sessions. It will also explore the risks associated with disclosure. Individual case studies of online use will provide transaction logs which will be examined to highlight any risks that arise. The study will work through the public library system to recruit a diverse range of individuals and to provide a safe environment for follow-up interviews. The study will also identify and interview subject experts to gain an understanding of how risk is handled in other industries (e.g. insurance, engineering safety, health) and to see how that might be applied to individual online behaviour.
The research builds on my doctoral work focused on the risks associated with access to personal data on online social networking services (Haynes 2015), which tested the idea that personal risk could be used as a way of assessing regulatory effectiveness (Haynes et al. 2016; Haynes & Robinson 2015).
Haynes, D., 2015. Risk and Regulation of Access to Personal Data on Online Social Networking Services in the UK. City University London.
Haynes, D., Bawden, D. & Robinson, L., 2016. A Regulatory Model for Personal Data on Social Networking Services in the UK. International Journal of Information Management, 36(6), pp.872–882.
Haynes, D. & Robinson, L., 2015. Defining User Risk in Social Networking Services. Aslib Journal of Information Management, 67(1), pp.94–115.
This Fellowship is supported by the Royal Academy of Engineering and the Office of the Chief Science Adviser for National Security under the UK Intelligence Community Postdoctoral Fellowship Programme.
December 2017